How PKI Technology Ensures Protection of Communication via Digital Channels
Fina PKI system
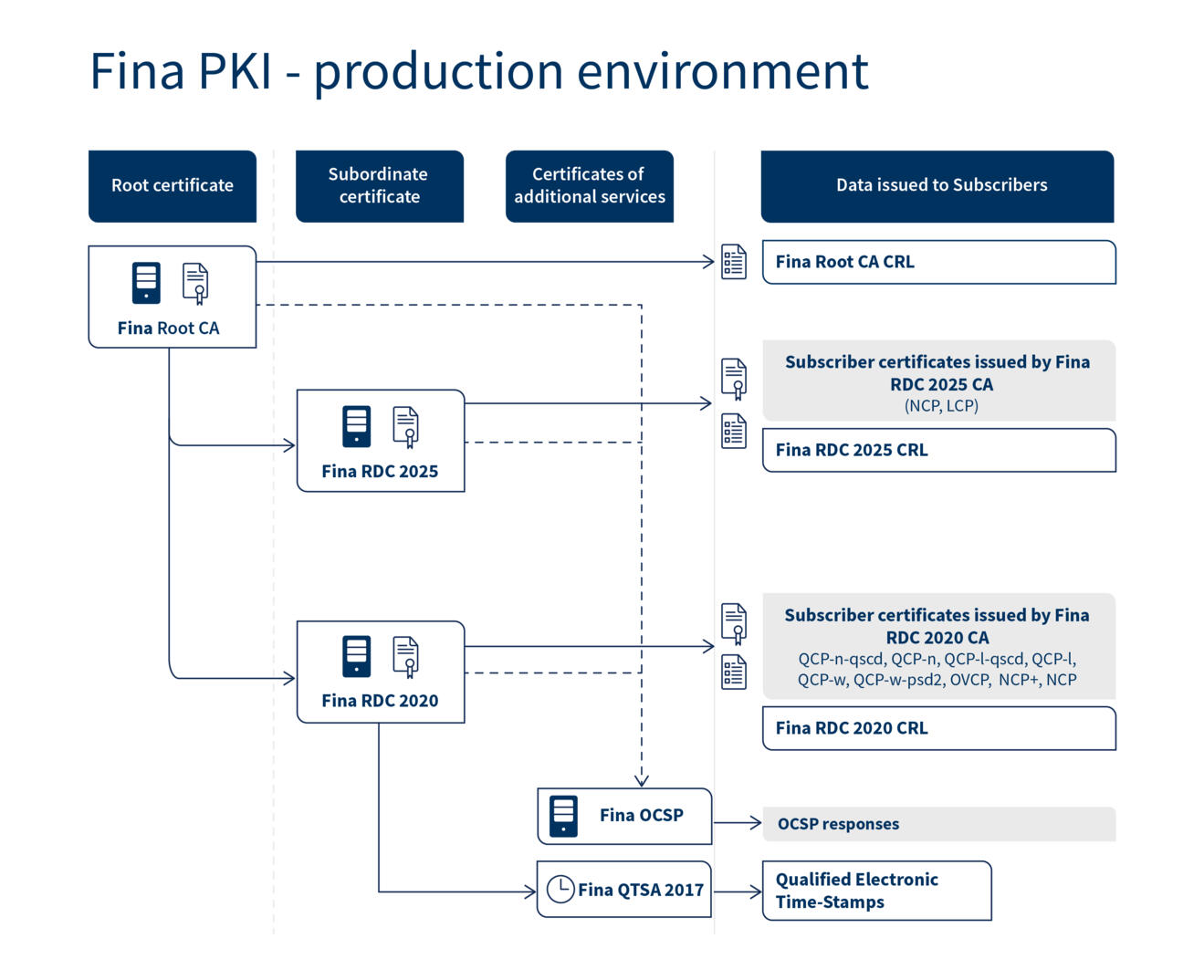
Fina’s production environment for issuing Digital Certificates and Qualified Electronic Time-Stamps
Characteristics of Fina’s production environment:
- Two-level architecture of Certification Autohrities (CA);
- Use of secure cryptographic algorithms and cryptographic keys;
- Certificate status verification service;
- Qualified Electronic Time-Stamp Service.
Digital Certificates and Qualified Electronic Time-Stamps issued using Fina’s production environment comply with the applicable EU and international standards concerning the issuance of Digital Certificates and Time Stamps, Electronic Signature standards and best practices.
The image presents a Digital Certificate and services provided by Fina’s two-level production environment for issuing Digital Certificates and Qualified Electronic Time-Stamps.
Two-tier architecture of Fina’s production Certification Authorities
The certificate issuing system comprises a Root Certification Authority (Root CA) which issues certificates to Subordinate Certification Authorities (Subordinate CA). Subordinate Certification Authorities issue certificates to end users.
Production environment for issuing Fina’s Digital Certificates includes:
- one Root Certification Authority: Fina Root CA; and
- two Subordinate Certification Authorities:
- Fina RDC 2020 and
- Fina RDC 2025.
Fina RDC 2020 issues qualified and normalized certificates, and Fina RDC 2025 issues normalized and lightweight certificates for:
- natural persons - citizens (personal certificates)
- natural persons associated with the business entity (business certificates) and
- IT equipment (systems, applications or services) associated with the business subject (business certificates for IT equipment).
Fina Root CA has issued and signed the certificates for the Fina RDC 2020 and Fina RDC 2025 Subordinate CAs.
Cryptographic algorithms and key lengths
Pursuant to the relevant Electronic Signature legislation, Fina uses prescribed secure cryptographic algorithms and cryptographic key lengths for issuing Certificates and Time-Stamps.
The SHA-256, RSA algorithm is used to compute hash value for signing certificates, CRLs and Time-Stamps.
The lengths of cryptographic RSA key pairs used are as follows:
- CA key pairs: 4096 bits, RSA,
- Subscriber key pairs: 2048 bits, RSA.
- Additionally, for certificates / qualified certificates for website authentication can also use 3072 or 4096 bits lengths Subscriber key pairs, RSA.
This ensures the security of and trust in issued Certificates and Qualified Electronic Time-Stamps
Characteristics of FINA’s production certificates
Fina Root CA Certificate
Fina Root CA is the root CA that issues and signs certificates for Fina's subordinated CAs (Fina RDC 2020 and Fina RDC 2025 CAs). Fina Root CA Certificate represents the "trust anchor" of Fina's two-tier architecture.
The Fina Root CA certificate contains an RSA public key with 4096-bit key size.
Certificates for the Fina RDC 2020 and Fina RDC 2025 CAs
The Fina RDC 2020 and Fina RDC 2025 Certificates are subordinate certificates of the Fina Root CA certificate. Certificates for Fina RDC 2020 and Fina RDC 2025 contain a 4096-bit RSA public key and they are signed by the Fina Root CA with a 4096-bit RSA private key using the SHA-256 and RSA cryptographic algorithms.
Characteristics of Subscriber Certificates
Subscriber Certificates are issued by Fina RDC 2020 and Fina RDC 2025.
All of Fina's production certificates and CAs` practices are described in the documents on the page "Legislation, Documents and Conformance Certificates".
Online certificate status verification service - FINA OCSP
Fina’s OCSP service titled Fina OCSP provides information about the statuses of certificates issued by Fina Root CA, Fina RDC 2020 and Fina RDC 2025. The access address for Fina OCSP is provided in the Authority Information Access extension of each Fina’s Production Certificate. Fina OCSP operates as recommended in IETF RFC 6960.
Fina OCSP signs responses by using a 2048-bit RSA private key and the SHA-256 and RSA cryptographic algorithms.
In addition to using Fina OCSP, certificate status may also be verified by retrieving CRLs. We recommend you use the OCPS service to verify certificate status and use CRL retrieval for status verification as an alternative verification method in case the OCSP service is unavailable.
Qualified Electronic Time-Stamping Service - FINA QTSA 2017
Qualified Electronic Time-Stamping Service is using for time-stamping of data, electronic records, electronic documents and the similar, by a Qualified Service Provider as a Trusted Third Party (TTP). A qualified electronic timestamp can be used to support an advanced and qualified electronic signature.
Authorized users who register for the service with Fina's digital certificate have the opportunity to use the Fina QTSA 2017 service.
Fina QTSA 2017 complies with the eIDAS regulation and supports the requirements of client applications for the issuance of electronic time stamps in accordance with ETSI EN 319 422 and IETF recommendation RFC 3161.
The certificate for signing the response of the Fina QTSA 2017 service is regularly issued every year, and electronic time stamps will be signed with the corresponding private key for one year. A new key pair will then be generated and a new certificate issued. The new private key will be used to sign electronic time stamps in the next year. Each certificate is valid for four years.
The documentation of Fina's systems for performing the services of issuing qualified time stamps can be found here.
Register of Digital Certificates
For the purpose of providing Certification services in Croatia, Fina has established through its Register of Digital Certificates a Public Key Infrastructure (PKI) including the following Certification Authorities (CA):
- Fina Root CA;
- Fina RDC 2025 CA and Fina RDC 2020 CA – for citizens and business entities (including state administration bodies).
For testing purposes, Fina has established a Demo Public Key Infrastructure (PKI) including the following Certification Authorities (CA):
- Fina Demo Root CA
- Fina Demo CA 2020 and
- Fina Demo CA 2014.
This website provides general information concerning Certification services and Certificate Lifecycle Management. Detailed information, basic rules and principles for providing certification services, which are in compliance with the legal regulations on electronic signatures in the Republic of Croatia, are available from the Legislation, Documents and Conformance Certificates.
Please refer to the Certificate Policy (CP) for detailed information, underlying rules and principles of providing Certification services in compliance with Regulation (EU) No 910/2014 of the European Parliament and of the Council on electronic identification and trust services for electronic transactions in the internal market, with corrections, amendments and/or supplements in force and in compliance with Act Implementing Regulation (EU) No 910/2014 of the European Parliament and of the Council of 23 July 2014 on electronic identification and trust services for electronic transactions in the internal market and repealing Council Directive 1999/93 / EC (Croatian Official Gazette 62/2017).